Secure RAG
Build RAG on Sensitive Data.
Without the Risk.
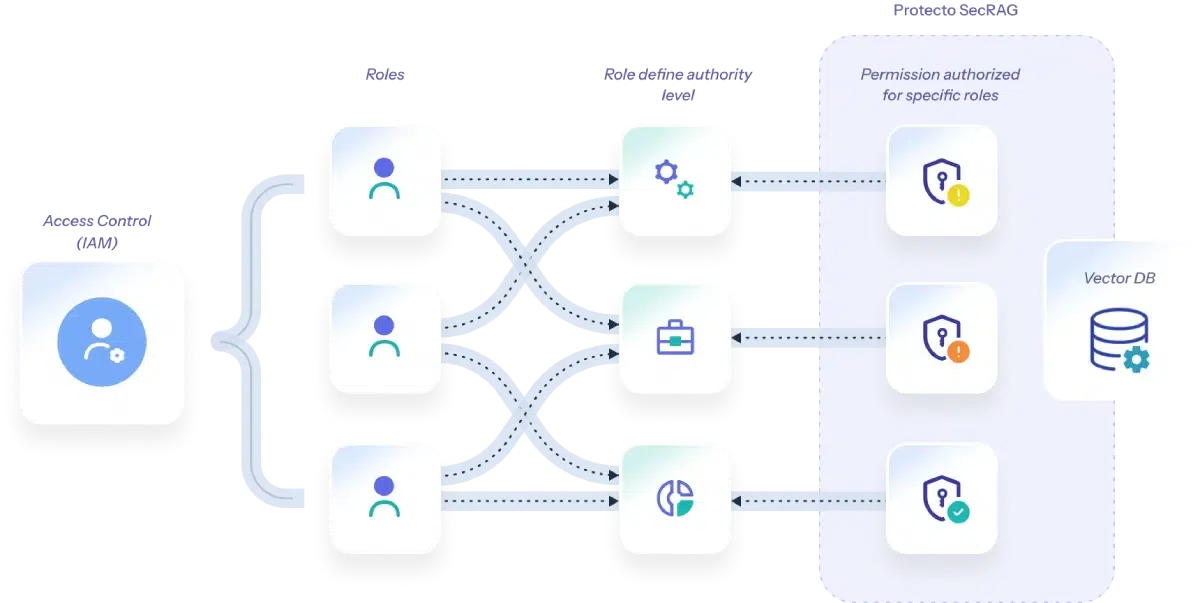
Add enterprise-grade role-based access control and sensitive data protection to any RAG pipeline in hours. No rework. No data leaks. No compliance risk.
- Trusted by Engineering Teams Building AI at Scale




The Problem
RAG Brings Power.
It Also Brings Risk.
Enterprise RAG runs on your real internal data. Without guardrails, that data is one query away from showing up in a model response it was never meant to be in.
Sensitive Data Leaks
RAG retrieves from real documents and generates answers from them. PII, PHI, and trade secrets can surface in model outputs. Customers whose data was supposed to stay private may find it in an AI response.
Regulatory Violations
HIPAA violations carry fines up to $1.9M per year. GDPR fines can reach 4% of global revenue. Most enforcement actions follow a breach, not a policy review. HIPAA, GDPR, CCPA, DPDP, and data residency laws all have specific requirements for how personal data can flow through AI systems.
Brand Reputation Loss
Toxic content, competitor mentions, and harmful AI outputs can reach customers before anyone catches them. Without active filtering, your AI is one bad response away from a PR incident.
How Protecto Works
Secure RAG in 5 Steps
Protecto drops into your existing AI data pipeline. No rearchitecting required.

Scan Data Sources
Protecto scans structured tables, unstructured documents, and free-text fields to find PII and PHI. It covers 50+ entity types without any configuration.
Mask Before Ingestion
Sensitive values get replaced with consistent pseudonyms before vectorization. The same name maps to the same token across documents, so retrieval stays coherent.
Filter Prompts and Responses
Every prompt and every LLM response is scanned before it moves on. Toxic content, competitor names, and any residual sensitive data get caught here.
Run Accurate AI
The LLM processes masked data and still produces accurate, coherent answers. Protecto has published benchmarks showing accuracy is fully preserved after masking.
Unmask for Authorized Users
When investigators need the original data, they access it through a secure, logged unmask workflow. Every access is recorded.
Why Protecto
Three Reasons Teams Choose Protecto for RAG
Most masking tools were built for data warehouses, not LLMs. Run them on RAG inputs and accuracy suffers. Protecto was built for AI workflows from the start.
01
Retains LLM Accuracy After Masking
Standard masking replaces values in ways that break context. Protecto uses consistent pseudonymization that keeps semantic relationships intact, so the LLM reasons correctly over masked data. No accuracy trade-off.
02
Highest PII Detection Accuracy
In independent F1 benchmarks, Protecto outperforms AWS Comprehend and Microsoft Presidio across 50+ PII entity types. You can add custom entity lists and define your own masking policies without retraining the model.
03
Built for Enterprise Scale
Synchronous APIs for low-latency prompt filtering. Async APIs for high-volume batch ingestion. Full audit logs, high availability, and disaster recovery included. Deploys on-prem or as SaaS.
Capabilities
What Protecto Covers
Six capabilities that work together, each covering a specific exposure point in your RAG pipeline.
Automatic PII and PHI Detection
Identifies sensitive data across text, structured databases, and unstructured documents. 50+ entity types supported out of the box.
Consistent Tokenization
Pseudonyms are consistent across sessions, keeping AI reasoning coherent across multi-turn conversations and multi-document retrieval.
Reversible Masking
Authorized users can unmask data through a secure, audited process. Designed for fraud teams, compliance reviewers, and support workflows.
Toxic Content Scanning
Detects hate speech, harmful language, and custom blocked terms in both prompts and responses before they reach users.
Custom Word Filtering
Block competitor names, internal code words, or any terms that carry reputational or legal risk. Policy-driven and fully configurable.
Flexible API Integration
Plug directly into any AI data pipeline at ingestion or inference time. Sync and async APIs with no added latency. Works across cloud providers and on-prem environments.
Success Story
How a Large Insurance Provider Used Secure RAG to Tackle $200B in Medical Overbilling
Healthcare. Compliance. AI.
Building a Privacy-Preserving Fraud Detection System
Medical billing errors (upcoding, unbundling, incorrect coding) cost the healthcare system hundreds of billions annually. A leading US insurance provider wanted to apply LLMs to detect discrepancies between clinical notes and billing codes at scale.
The problem: every claim record contained PHI. Running that data through an LLM without masking it first would break HIPAA. The team needed a way to let the AI see the clinical patterns without seeing the patients.
- Protecto scanned and masked all PHI within the clinical notes dataset before ingestion into the data pipeline.
- Masked notes were vectorized and stored. LLMs ran similarity searches to flag billing discrepancies.
- Fraud analysts accessed original data via Protecto's secure unmask workflow when investigation required identifiable records.
- Full HIPAA compliance maintained throughout. LLM accuracy unaffected by the masking process.
Security and Compliance
Compliance isn't a checkbox.
It's built into the platform.
Every Protecto deployment includes audit logs for every scan, mask, and unmask event. We sign BAAs for HIPAA. We support data residency and air-gapped deployments for strict sovereignty requirements.
Adopt AI. Not AI Risk.
Your RAG pipeline is already in production. The question is whether your data privacy is. Protecto takes minutes to integrate.
- SOC2 Certified
- HIPAA Compliant
- GDPR Ready
- ISO 27001